- Integrations
- Auth0
Integrations
Auth0
This tutorial demonstrates how to integrate Criipto Verify with Auth0.
This tutorial demonstrates how to integrate Criipto Verify with Auth0. The following steps are required to complete your first login:
- Register your Auth0 tenant in Criipto Verify
- Configure OAuth2 Code Flow
- Create Auth0 connections
- Integrate your application with Auth0
In the following, you'll first configure Criipto Verify, then Auth0, and finally complete the Criipto Verify configuration with the information you get from Auth0. Once everything's configured, you can test your integration from Auth0.
Register your Auth0 tenant in Criipto Verify
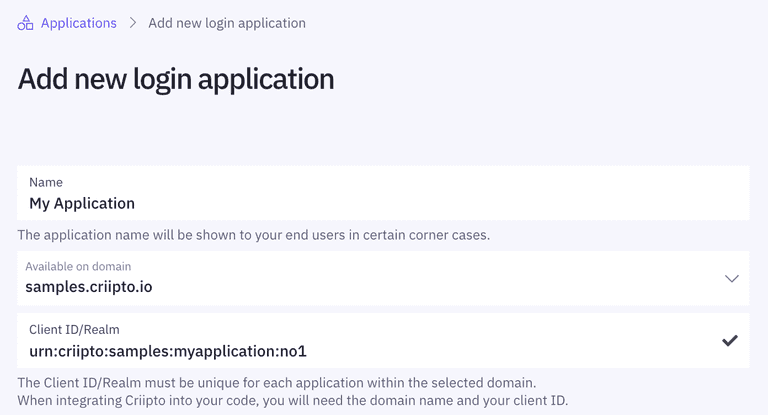
First, you must register your Auth0 tenant as an application in Criipto Verify.
Once you register your Auth0 tenant, you will also need some of the information for configuring Auth0 to communicate with Criipto Verify. You get these details from your application settings in the dashboard.
Specifically, you need the following information to integrate with Auth0:
- Client ID to identify your Auth0 tenant to Criipto Verify. In the case below, we chose
urn:criipto:samples:myapplication:no1 - Domain on which you will be communicating with Criipto Verify. It could be, for example,
samples.criipto.io - Client secret is needed if you choose the back-channel approach. The secret is generated when you configure OAuth2 Code Flow.
Configure OAuth2 Code Flow
If you are registering a new application, please save the initial configuration first.
After saving, you can configure the OAuth2 Code Flow for this application by following the three steps:
- Go to the OpenID Connect section of your Application settings and Enable OAuth2 Code Flow.
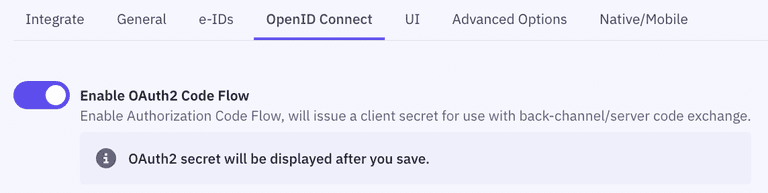
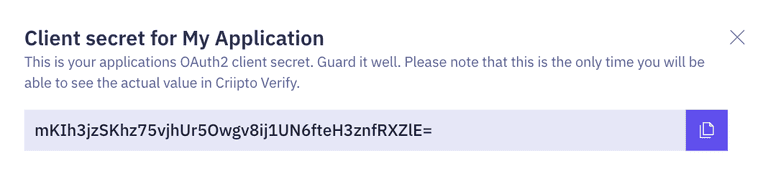
- Copy the generated client secret. Note that this is the only time you will be shown the actual value of the client secret. Criipto only stores this as a hashed value, which means you cannot retrieve the value once it has been generated and stored.
- Set the user info response strategy to
plainJsonto enable retrieval of plain JSON user information from the/oauth2/userinfoendpoint.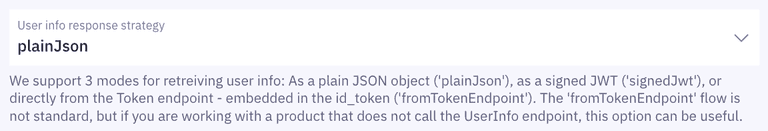 Note that some libraries do not support the final
Note that some libraries do not support the final userinforequest. In those cases, you will need to fetch the user data directly from thetokenendpoint as opposed to theuserinfoendpoint. You can do this by choosingfromTokenEndpointas aUser info response strategy.
Criipto Verify supports four modes for retrieving user information:
- Plain JSON object (
plainJson): User information is returned from theuserinfoendpoint as a standard JSON object. - Signed JWT (
signedJwt): User information is returned from theuserinfoendpoint as a digitally signed JSON Web Token. - Signed and encrypted JWT (
signedAndEncryptedJwt): User information is returned from theuserinfoendpoint as a signed and encrypted JSON Web Encryption(JWE) object. - Directly from the
tokenendpoint, embedded in theid_token(fromTokenEndpoint). ThefromTokenEndpointflow is not standard, but can be useful if you are working with a product that does not call theuserinfoendpoint.
Create Auth0 connections
You can leverage either an Enterprise Connection, or a Custom Social Connection to connect Criipto Verify with Auth0.
Login-method specific endpoints
To integrate Criipto Verify with Auth0, you create an Auth0 OpenID Connect(OIDC) connection to communicate with Criipto Verify. Because Auth0 will not pass the acr_values to Criipto Verify, you will have to create a new connection for every eID option that you intend to use. (acr_values is a parameter in the /authorize request to Criipto Verify needed to specify which kind of eID is requested).
For those cases, you can leverage our login-method specific metadata endpoints (for Enterprise Connections) and authorize URLs (for Custom Social Connections). Each of these contain an embedded and base64-encoded variant of the "raw" value normally supplied in the acr_values.
Syntax:
- Issuer metadata endpoint:
https://yourdomain.criipto.id/BASE64(acr_values)/.well-known/openid-configuration - Authorize URL:
https://yourdomain.criipto.id/BASE64(acr_values)/oauth2/authorize
For example, the acr_values of Norwegian BankID login method is urn:grn:authn:no:bankid. This translates to dXJuOmdybjphdXRobjpubzpiYW5raWQ= in base64 (UTF-8 charset), so the syntax will be:
- Issuer metadata endpoint:
https://yourdomain.criipto.id/dXJuOmdybjphdXRobjpubzpiYW5raWQ=/.well-known/openid-configuration - Authorize URL:
https://yourdomain.criipto.id/dXJuOmdybjphdXRobjpubzpiYW5raWQ=/oauth2/authorize
Choose the specific login method
Below is a list of supported login methods with the corresponding base64 encoded acr_values. Choose the ones you intend to use.
| Login method | acr_values | base64 encoded |
|---|---|---|
| Norwegian BankID | ||
| Mobile or Web (user choice): | urn:grn:authn:no:bankid | dXJuOmdybjphdXRobjpubzpiYW5raWQ= |
| BankID Biometrics (level substantial): | urn:grn:authn:no:bankid:substantial | dXJuOmdybjphdXRobjpubzpiYW5raWQ6c3Vic3RhbnRpYWw= |
| Norwegian Vipps Login | ||
| Login with Vipps app: | urn:grn:authn:no:vipps | dXJuOmdybjphdXRobjpubzp2aXBwcw== |
| Swedish BankID | ||
| All options (user chooses): | urn:grn:authn:se:bankid | dXJuOmdybjphdXRobjpzZTpiYW5raWQ= |
| Same device: | urn:grn:authn:se:bankid:same-device | dXJuOmdybjphdXRobjpzZTpiYW5raWQ6c2FtZS1kZXZpY2U= |
| Another device (aka mobile): | urn:grn:authn:se:bankid:another-device | dXJuOmdybjphdXRobjpzZTpiYW5raWQ6YW5vdGhlci1kZXZpY2U= |
| QR code: | urn:grn:authn:se:bankid:another-device:qr | dXJuOmdybjphdXRobjpzZTpiYW5raWQ6YW5vdGhlci1kZXZpY2U6cXI= |
| Danish MitID | ||
| Level low: | urn:grn:authn:dk:mitid:low | dXJuOmdybjphdXRobjpkazptaXRpZDpsb3c= |
| Level substantial: | urn:grn:authn:dk:mitid:substantial | dXJuOmdybjphdXRobjpkazptaXRpZDpzdWJzdGFudGlhbA== |
| MitID Erhverv (MitID Business): | urn:grn:authn:dk:mitid:business | dXJuOmdybjphdXRobjpkazptaXRpZDpidXNpbmVzcw== |
| Finnish Trust Network | ||
| BankID: | urn:grn:authn:fi:bankid | dXJuOmdybjphdXRobjpmaTpiYW5raWQ= |
| Mobile certificate (Mobiilivarmenne): | urn:grn:authn:fi:mobile-id | dXJuOmdybjphdXRobjpmaTptb2JpbGUtaWQ= |
| Both of the above: | urn:grn:authn:fi:all | dXJuOmdybjphdXRobjpmaTphbGw= |
| Itsme | ||
| Basic: | urn:grn:authn:itsme:basic | dXJuOmdybjphdXRobjppdHNtZTpiYXNpYw== |
| Advanced: | urn:grn:authn:itsme:advanced | dXJuOmdybjphdXRobjppdHNtZTphZHZhbmNlZA== |
| Belgium | ||
| Verified e-ID: | urn:grn:authn:be:eid:verified | dXJuOmdybjphdXRobjpiZTplaWQ6dmVyaWZpZWQ= |
Enterprise Connection
You can connect Auth0 to Criipto Verify by creating an OIDC Enterprise Connection. You create an OIDC connection for every login method you intend to use.
Create the OIDC connection(s)
- Go to Auth0 dashboard for your tenant and under Authentication choose Enterprise.
- Select OpenID Connect and create a new connection.
- Enter Connection name.
- Under Issuer URL enter the login-method specific URL, as described above.
- Under Client ID enter the Client ID/Realm from your Criipto Verify application.
- Copy the Callback URL generated by Auth0 and enter it under Callback URLs in Criipto Verify application management.
- Back in the Auth0 dashboard, create a connection by clicking Create.
- After the connection is created, go to the Settings tab.
- Choose Front Channel or Back Channel as a Type, depending on how you intend to integrate it with your application.
- you should choose Front Channel only if you are developing a pure SPA application. Otherwise, choose Back Channel.
- If you chose Back Channel as a Type, enter the Client Secret generated by Criipto Verify when you enabled the OAuth2 Code Flow.
- Select Save Changes.
- Make sure to enable the created connection for your Auth0 application.
After you save a connection, you may get an error: "Error! Something happened while trying to save your connection: Issuer metadata missing the following attributes: token_endpoint".
This is due to a bug in Auth0's frontend, nothing to worry about. In this case, under the Issuer URL select Show Issuer Details and under Token Endpoint enter https://<YOUR COMPANY>.criipto.id/oauth2/token
If you are creating multiple connections, you have to enter Callback URL only once. It will be the same for every OpenID Connect connection.
Test the connection
To test your OpenID Connect connection, go back to the list of all OpenID Connect connections and select Try button on the right side of the connection you want to test. You will need a test user to perform testing.
Custom Social Connection
Alternatively, you can leverage a Custom Social Connection to integrate with Criipto Verify via OpenID Connect. Create an OIDC connection for every login method you intend to use.
Create the OIDC connection(s)
- Go to Auth0 dashboard for your tenant and under Authentication choose Social.
- Select Create Connection, go to the bottom of the list, then choose Create Custom.
- Enter Connection name.
- Under Authorization URL enter a login-method specific authorize URL to which your users will be redirected to log in to your application, e.g.
https://yourdomain.criipto.id/dXJuOmdybjphdXRobjpubzpiYW5raWQ=/oauth2/authorize?scope=openid&client_id=urn:criipto:samples:no1&redirect_uri=https://jwt.io&response_type=code - Under Token URL, enter your token endpoint:
https://yourdomain.criipto.id/oauth2/token - Under Client ID enter the Client ID/Realm from your Criipto Verify application.
- Under Client Secret enter the Client Secret generated by Criipto Verify when you enabled the OAuth2 Code Flow.
- Add the required Fetch User Profile Script using your
userInfoendpoint, e.g.:
function fetchUserProfile(accessToken, context, callback) {
request.get(
{
url: 'https://yourdomain.criipto.id/oauth2/userinfo',
headers: {
Authorization: 'Bearer ' + accessToken,
},
},
(err, resp, body) => {
if (err) {
return callback(err);
}
if (resp.statusCode !== 200) {
return callback(new Error(body));
}
let bodyParsed;
try {
bodyParsed = JSON.parse(body);
} catch (jsonError) {
return callback(new Error(body));
}
const profile = {
user_id: bodyParsed.uuid,
name: bodyParsed.name,
};
callback(null, profile);
}
);
}
- Create a connection by clicking Create.
- Make sure to enable the created connection for your Auth0 application.
- Lastly, add Auth0's callback URL (
https://{yourAuth0Domain}/login/callback) to your Criipto Verify application. Go to your Criipto Dashboard, and enter the Auth0 Callback URL under Callback URLs in Criipto Verify application management.
Test the connection
Test your Custom Social Connection by clicking the Try Connection button located in the top right corner.
Test users
Almost all eID types have a notion of test users and real users.
Real users are real people logging in to a web site, thus voluntering their real name and typically also a social security number, SSN.
Test users are either created by you for the occasion, or we provide you with access to already created test users.
You may read more in the section on eIDs
Integrate your application with Auth0
How to integrate your application with Auth0 depends on the technology you are working with. Refer to the Auth0 quickstart guide for more details.